CISA Warns Federal Agencies About CopyFail Linux Vulnerability: Critical CVE-2026-31431 Requires Immediate Action
CISA added CVE-2026-31431 to its Known Exploited Vulnerabilities (KEV) catalog on May 1, 2026, confirming active exploitation of the CopyFail Linux vulnerability across federal and enterprise environments. This high-severity local privilege escalation flaw in the Linux kernel’s cryptographic subsystem demands immediate attention from organizations running affected systems.
This guide covers federal agency requirements under Binding Operational Directive 22-01, technical details of the CopyFail security flaw, and practical mitigation strategies for enterprise infrastructure. The content addresses federal IT administrators, enterprise security teams, and compliance officers managing Linux systems who must understand both the technical threat and regulatory obligations this vulnerability creates.
CISA issued urgent guidance requiring federal agencies to patch the CopyFail vulnerability by May 15, 2026, due to active exploitation enabling root privilege escalation on virtually all Linux distributions running kernels from 2017 onward.
By the end of this article, you will understand:
The technical mechanics behind CVE-2026-31431 and why it poses significant risks to Linux endpoints
CISA’s compliance requirements under BOD 22-01 and consequences of non-compliance
Step-by-step vulnerability assessment procedures for affected systems
Practical remediation strategies including patching and alternative mitigation controls
Solutions for common implementation challenges in federal enterprise environments
Understanding the CopyFail Vulnerability
The Copy Fail vulnerability, tracked as CVE-2026-31431, is a high-severity local privilege escalation vulnerability affecting the Linux kernel’s cryptographic subsystem, with a CVSS score of 7.8. This score indicates a significant impact on confidentiality, integrity, and availability, reflecting the critical nature of the flaw. The vulnerability enables unprivileged local users to gain root privileges through a deterministic exploit that requires no race conditions or system-specific offsets.

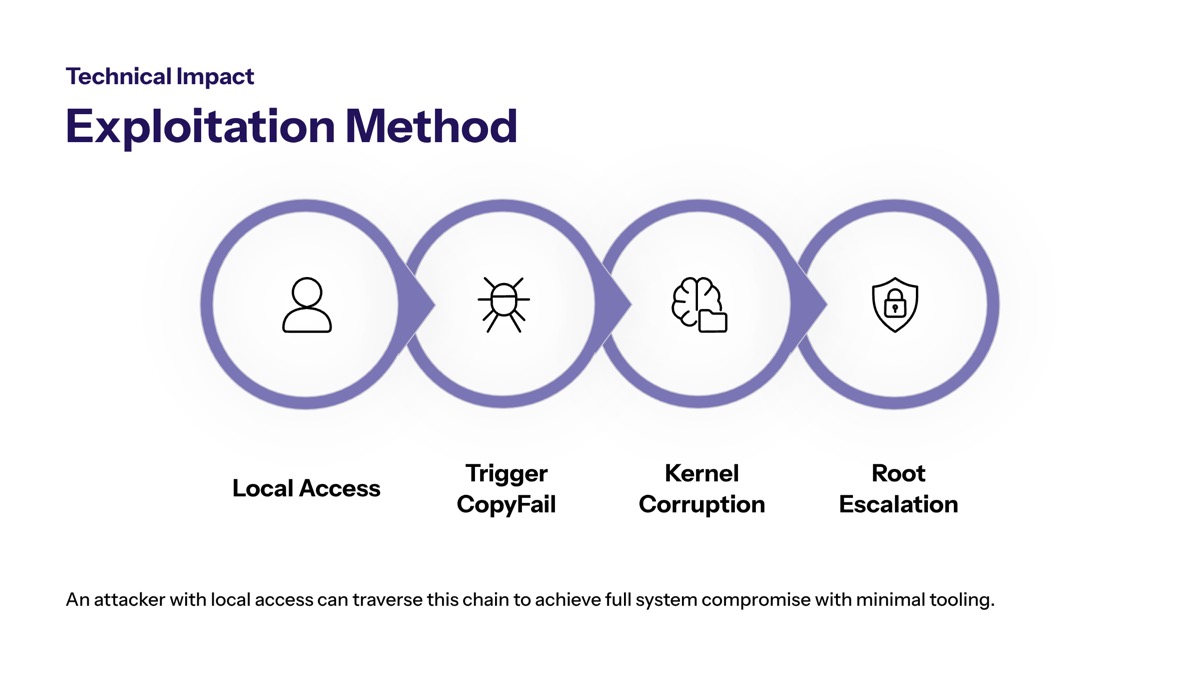
Technical Impact and Exploitation Method
The security flaw originates from a logic error in the AF_ALG module’s algif_aead component, specifically in how the kernel handles in-place AEAD (Authenticated Encryption with Associated Data) operations combined with the splice() system call. This incorrect resource transfer between spheres vulnerability allows attackers to perform a controlled 4-byte write directly into the kernel page cache.
Successful exploitation of the Copy Fail vulnerability can lead to full root privilege escalation, allowing attackers to bypass security controls and potentially compromise multi-tenant environments. The in-memory only modification technique targets readable files such as setuid binaries (like /usr/bin/su), corrupting them in the page cache without altering underlying disk contents. When the modified binary executes, the attacker achieves root access.
Exploitation of CopyFail can be performed with a small, roughly 732-byte Python script to execute controlled writes in the page cache. This Python-based exploit demonstrates cross-platform applicability—the same exploit binary works unmodified across Ubuntu, RHEL, Amazon Linux, and other major Linux distros. CopyFail is highly reliable, reportedly functioning without reliance on race conditions or specific system offsets, making it a frequent attack vector for malicious cyber actors.
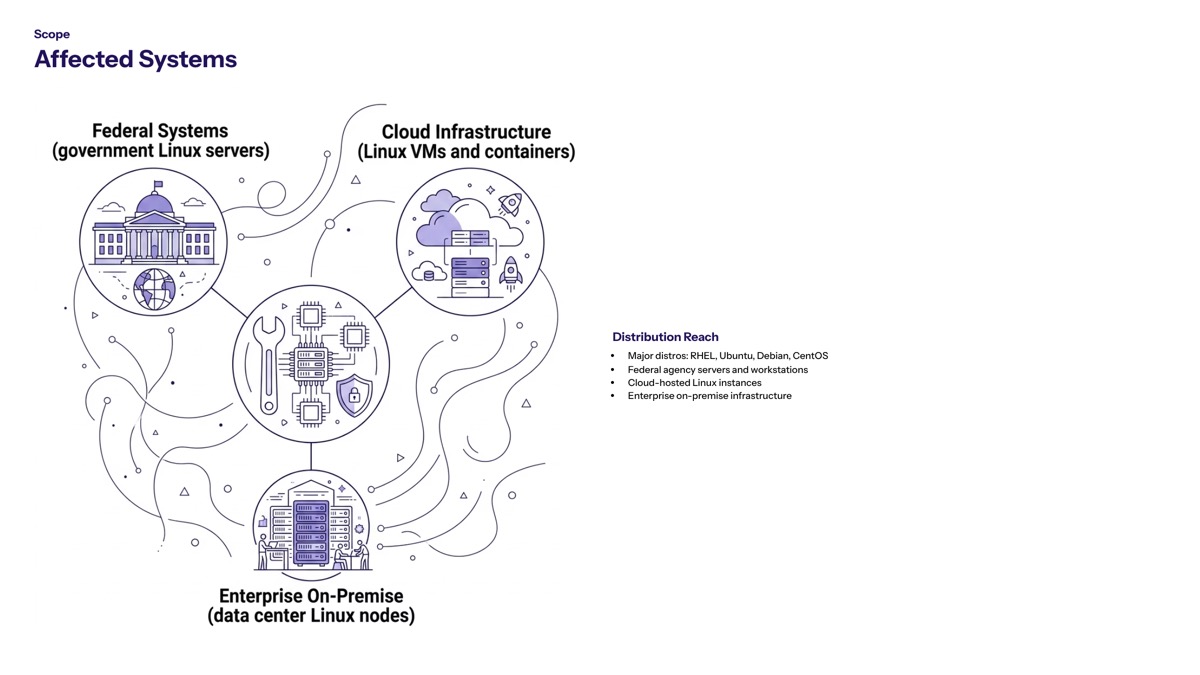
Affected Systems and Distribution Scope
The vulnerability affects virtually all Linux distributions running kernels released from 2017 until patched versions are applied, including Ubuntu, Amazon Linux, Red Hat Enterprise Linux, and SUSE, among others. Any vulnerable kernel version from 4.14 onward carries this Linux security vulnerability, meaning unpatched Linux systems across federal agencies have been exposed for more than a decade.
Federal agency infrastructure likely contains numerous components running affected systems—from production servers and development environments to containerized workloads in cloud services. The flaw was discovered by researchers at Xint Code and Theori and reported to the Linux kernel team in March 2026, with public disclosure and proof of concept (POC) release occurring on April 29, 2026.
Understanding CISA’s response to this privilege escalation vulnerability requires examining why the infrastructure security agency prioritized immediate action and what compliance obligations federal agencies now face.
CISA’s Federal Agency Directive
CISA maintains the Known Exploited Vulnerabilities catalog as the authoritative source for vulnerabilities confirmed to be actively weaponized by threat actors. When CVE-2026-31431 entered this exploited vulnerabilities catalog, it triggered mandatory remediation requirements for all federal civilian executive branch agencies under existing directives.
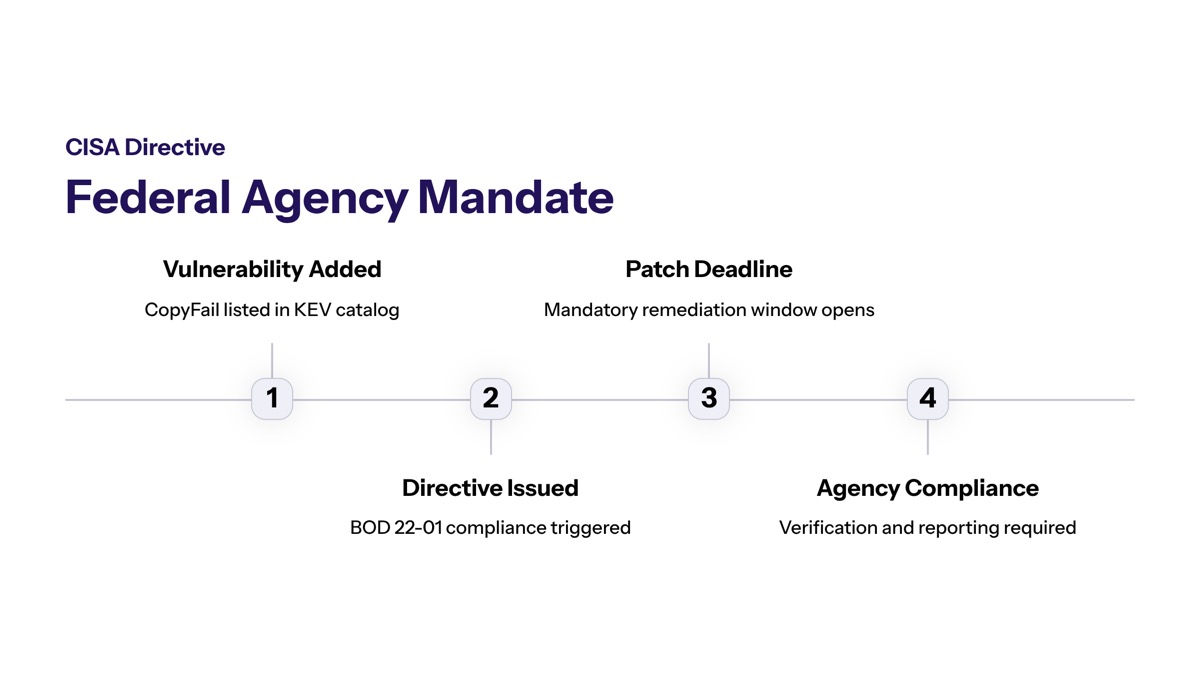
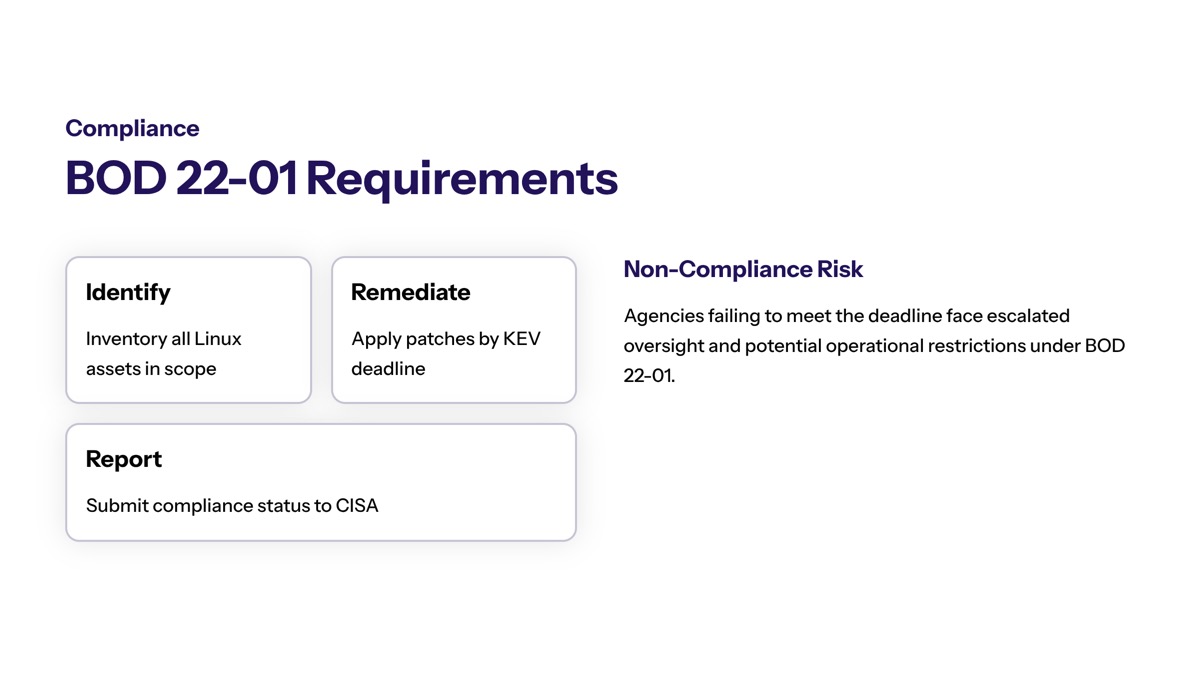
BOD 22-01 Compliance Requirements
Under Binding Operational Directive (BOD) 22-01, all Federal Civilian Executive Branch agencies are mandated to remediate the vulnerability by May 15, 2026. This directive—titled “Reducing the Significant Risk of Known Exploited Vulnerabilities”—requires agencies to patch immediately or discontinue use of affected systems when patches cannot be applied within the compliance window.
Federal IT teams must document their remediation efforts, report compliance status through established channels, and maintain audit trails demonstrating completed patching or approved mitigations. Non-compliance exposes agencies to security risks and potential oversight actions. Systems operated on behalf of agencies by contractors or cloud providers fall within scope, requiring coordination across organizational boundaries.
Active Exploitation Evidence
CISA added CVE-2026-31431 to its Known Exploited Vulnerabilities (KEV) catalog, confirming it is actively exploited in hacking campaigns targeting vulnerable systems. Threat actors leverage the CopyFail flaw to establish initial persistence after gaining any form of untrusted code execution on target systems.
The attack chain typically begins with remote code execution through a separate vulnerability or compromised credentials providing secure shell access. Once local access exists, the same script achieving root privilege escalation works across mainstream Linux distribution deployments without modification. Successful exploitation leads to complete system compromise, enabling lateral movement through federal networks and potential access to sensitive data or critical infrastructure.
Enterprise and Private Sector Implications
Organizations outside federal mandates should treat CISA guidance as authoritative intelligence about active threats. The vulnerability poses a significant risk in multi-tenant cloud environments because the page cache is shared across hosts, potentially allowing container breakout. Successful exploitation of the Copy Fail vulnerability can lead to full root privilege escalation, facilitating container breakout and lateral movement within shared environments, making it particularly dangerous in cloud and CI/CD environments.
Healthcare organizations subject to HIPAA, financial institutions under PCI DSS, and defense contractors maintaining compliance with NIST frameworks face regulatory expectations to address known exploited vulnerabilities promptly. Organizations should use the CISA Known Exploited Vulnerabilities (KEV) catalog as an input to their vulnerability management prioritization framework to effectively manage vulnerabilities and keep pace with threat activity.
Security teams must now translate these requirements into systematic assessment and remediation procedures across their Linux infrastructure.
Vulnerability Assessment and Remediation Procedures
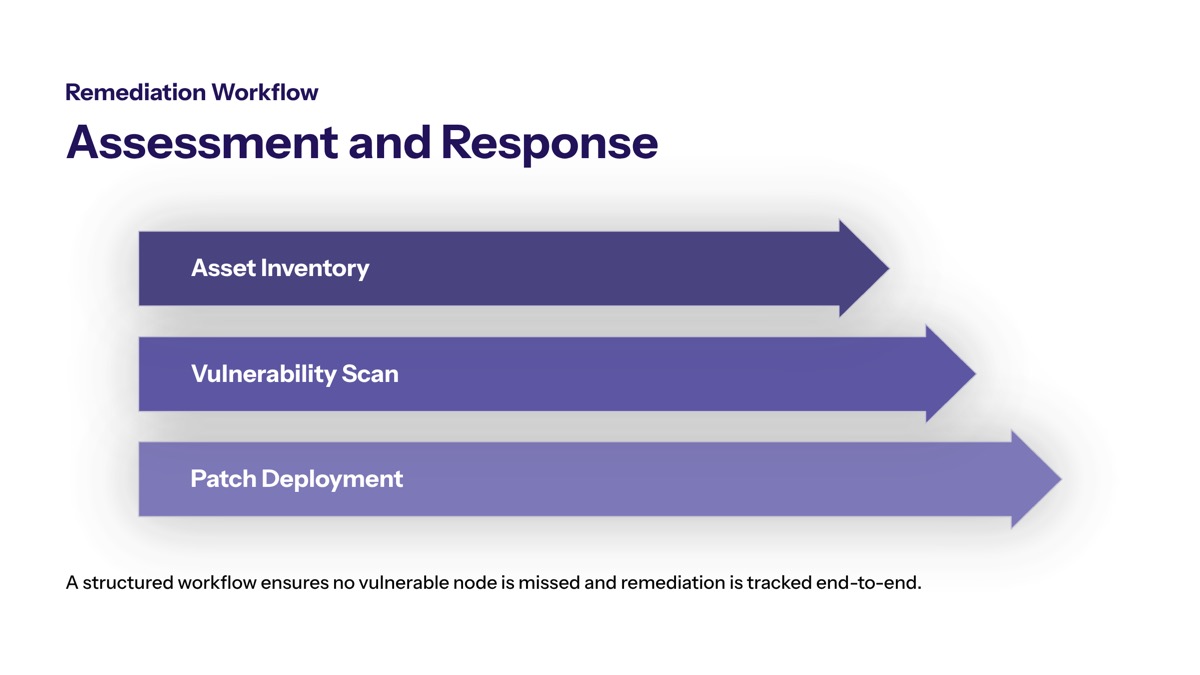
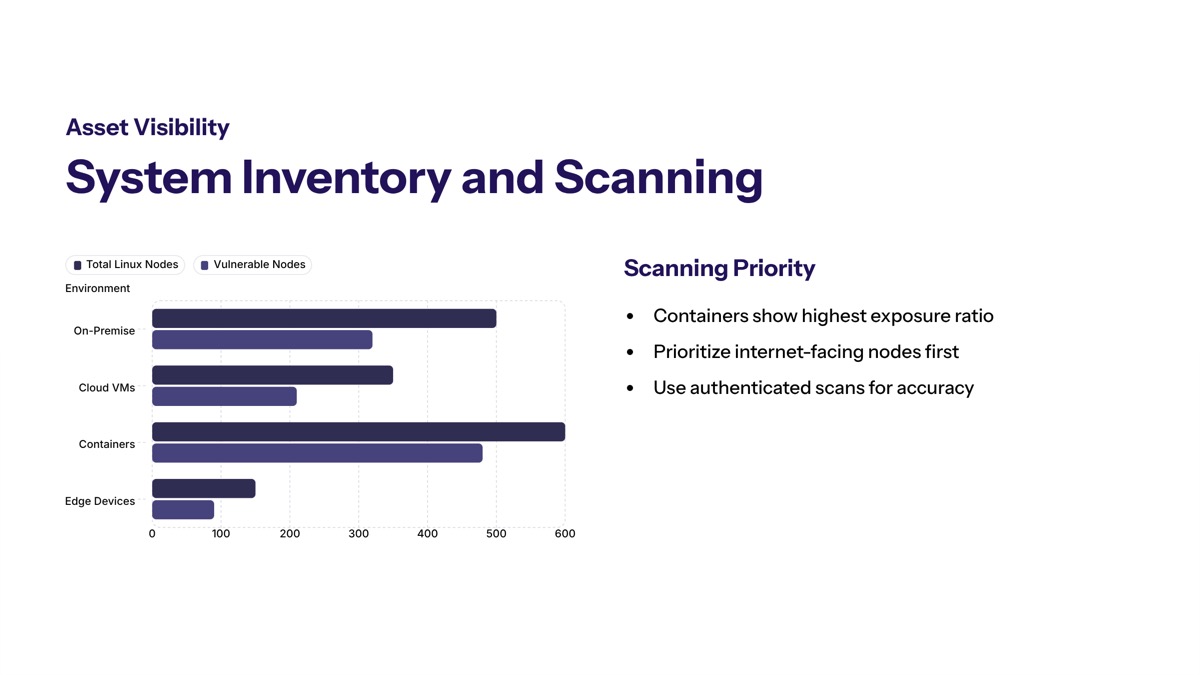
Addressing CVE-2026-31431 requires a methodical approach combining asset discovery, vulnerability validation, patch deployment, and documentation. Federal enterprise environments often contain diverse Linux deployments spanning physical servers, virtual machines, containers, and embedded devices, each requiring appropriate assessment.
System Inventory and Vulnerability Scanning
Comprehensive scanning becomes necessary when compliance deadlines mandate documentation of all affected systems. Follow these steps to establish your vulnerability baseline:
Catalog all Linux systems including servers, containers, and embedded devices—verify kernel versions via uname -r and check distribution versions across all Linux endpoints
Identify whether CONFIG_CRYPTO_USER_API_AEAD is enabled by examining /boot/config-$(uname -r) or /proc/config.gz to determine if the vulnerable module is present
Assess network accessibility and potential attack paths by mapping which systems allow unprivileged user access, host multi-tenant workloads, or run web applications susceptible to initial compromise
Prioritize systems based on criticality and exposure level—CI/CD build hosts, container orchestration nodes, and internet-facing systems warrant immediate attention
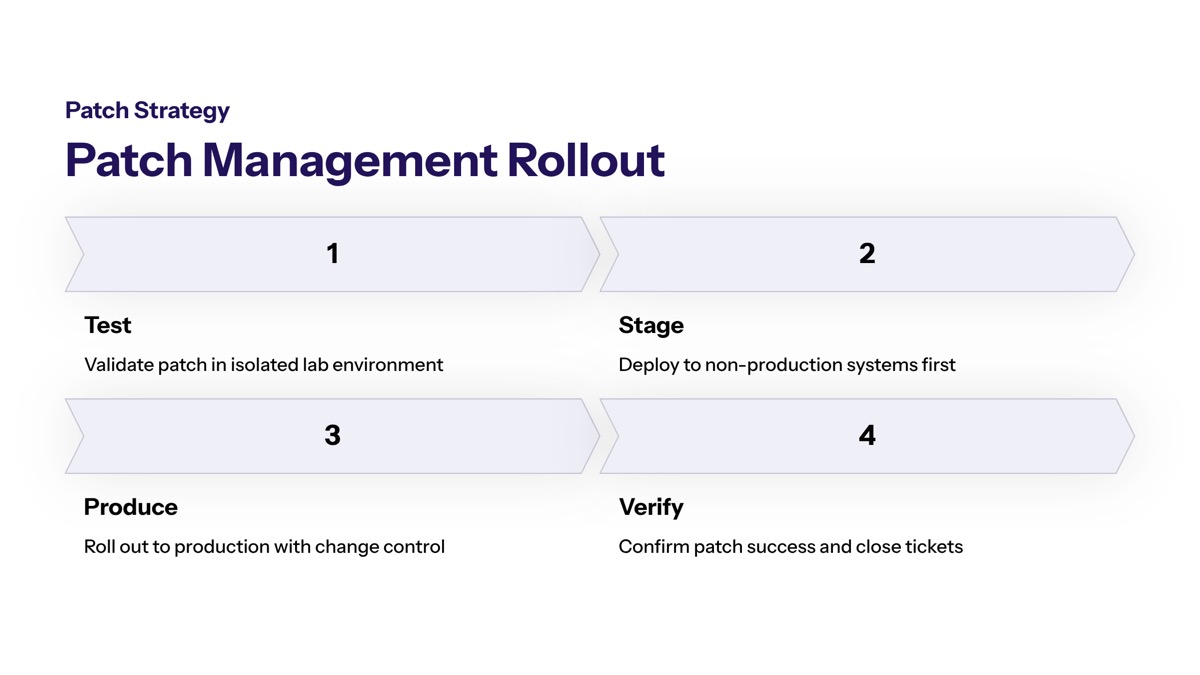
Patch Management Strategy
Major Linux distros patched the vulnerability following upstream kernel fixes in commit a664bf3d603d. Fixed kernel versions include 6.18.22, 6.19.12, and all releases from 7.0 forward. Each Linux distribution shipped updated packages through standard repositories:
Distribution | Patch Status | Update Command |
|---|---|---|
Ubuntu 24.04 LTS | Available | apt update && apt upgrade linux-image-* |
RHEL 10.1 | Available | dnf update kernel |
Amazon Linux 2023 | Available | dnf update kernel |
SUSE 16 | Available | zypper update kernel-default |
It is recommended to review available mitigation suggestions for the specific Linux distribution being used prior to applying any suggested mitigation options for vulnerabilities like Copy Fail. Testing procedures should validate patches in staging environments before production deployment. Document rollback procedures and ensure system availability planning accounts for required reboots to load fixed kernels.
Alternative Mitigation Controls
Immediate actions to mitigate the Copy Fail vulnerability include disabling the affected feature, implementing network isolation, and applying access controls to limit exposure when immediate patching isn’t feasible.
To mitigate the risk, administrators can disable the affected algif_aead module if immediate patching is not possible:
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aeadBefore disabling AF_ALG functionality, assess whether any applications depend on kernel cryptographic interfaces. The PackageKit daemon and certain security tools may require this functionality. Implement seccomp filters restricting AF_ALG socket creation in containerized workloads to prevent exploitation paths.
Network isolation strategies include restricting which users can establish local sessions and monitoring for suspicious activity targeting setuid binaries. Microsoft Defender and similar endpoint detection tools should be configured to alert on unexpected privilege escalation attempts.
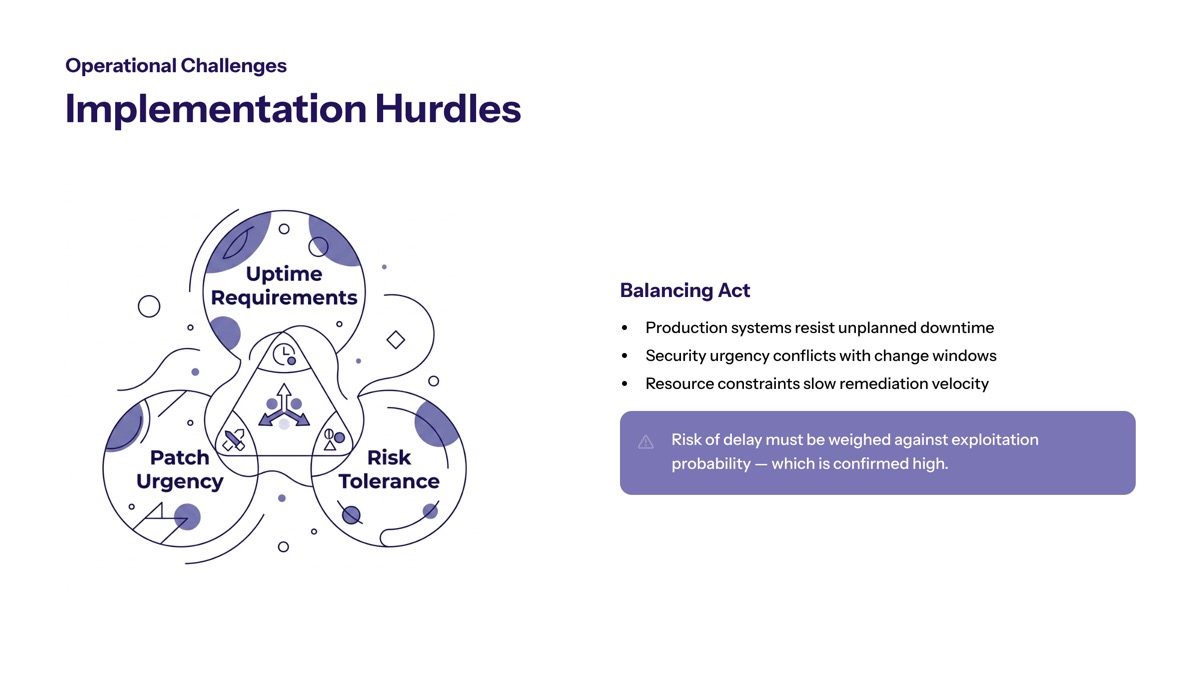
Organizations must choose between immediate patching—the preferred approach—versus temporary controls based on system criticality, available maintenance windows, and acceptable risk levels. Following vendor instructions for your specific environment ensures mitigations don’t introduce operational problems.

Common Implementation Challenges and Solutions
Emergency patching at scale presents obstacles that federal agencies and enterprises must navigate while meeting compliance deadlines. Understanding common challenges enables proactive planning.
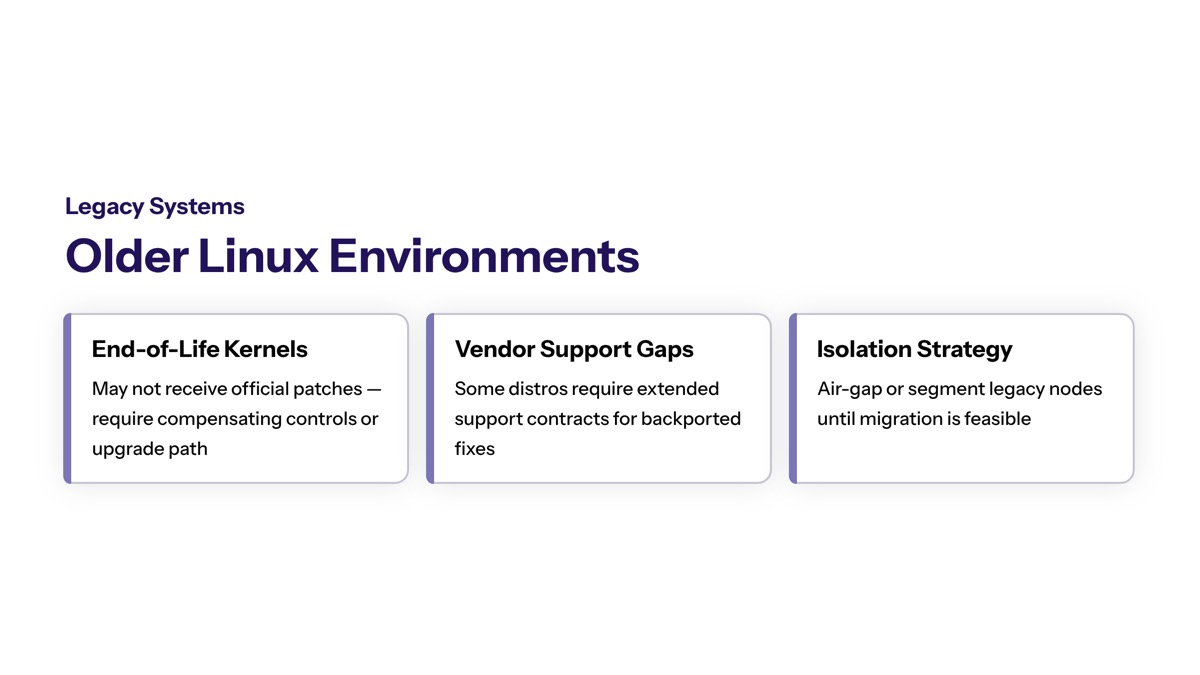
Legacy System Compatibility
Some Linux systems run end-of-life kernels without available patches. For these systems:
Conduct assessment procedures to determine if the vulnerable module exists. If algif_aead is built into the kernel rather than loaded as a module, the module-disabling workaround won’t function—network segmentation becomes the primary control. Implement enhanced monitoring for privilege escalation attempts on systems that cannot be patched, and establish network isolation preventing lateral movement from potential Dirty Frag or similar exploitation scenarios.
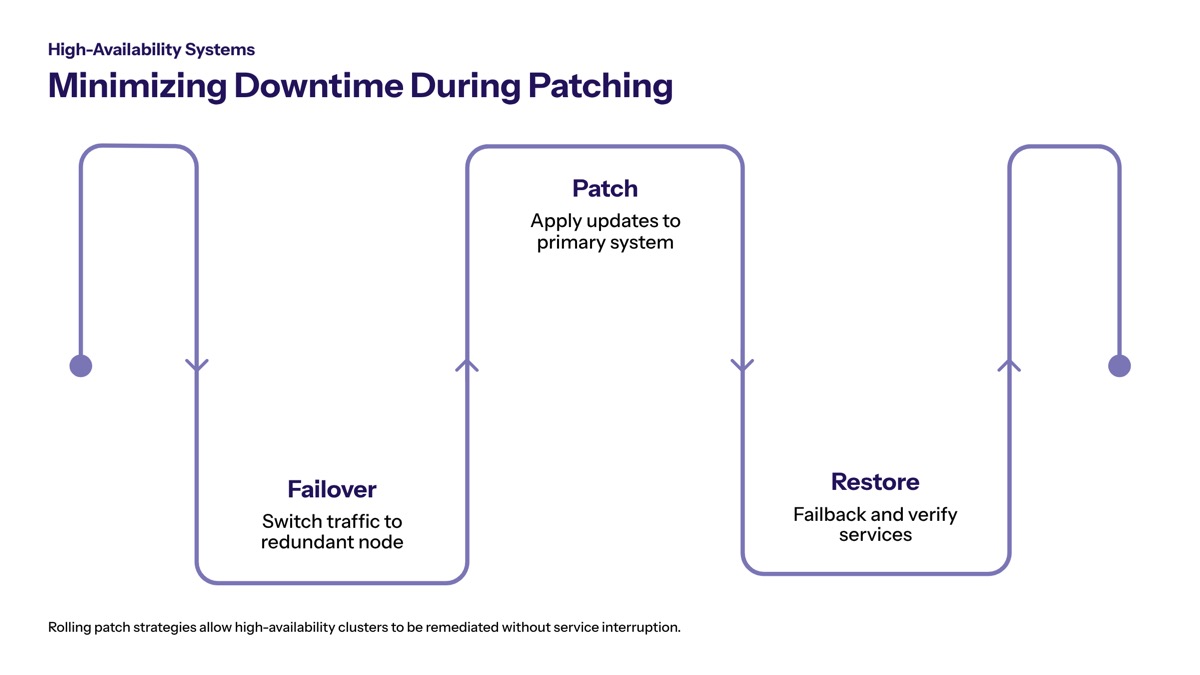
High-Availability System Downtime
Clustered systems and load-balanced environments require careful coordination to maintain service availability during patching:
Rolling update procedures allow individual nodes to be patched and rebooted while others maintain service. For systems supporting four root shells or similar high-availability configurations, stage updates during low-traffic windows with validated rollback procedures. Business continuity planning should account for the May 15th deadline while minimizing service disruption.
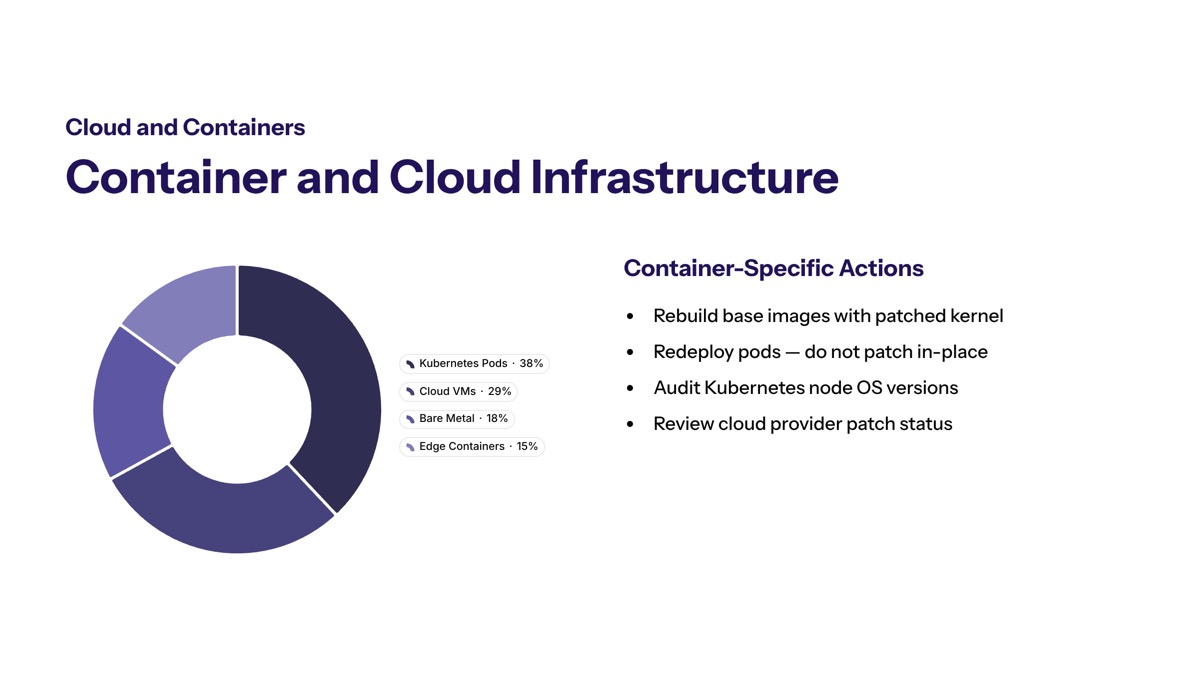
Container and Cloud Infrastructure
Cloud environments introduce shared responsibility considerations. Container base images must be updated to include patched kernels, and container registries should be audited to prevent deployment of vulnerable images.
For Kubernetes environments, host kernel patching remains the organization’s responsibility even when managed container services handle orchestration. The vulnerability enables multi-tenant compromise through shared page cache exploitation, meaning a single compromised container could facilitate container breakout to achieve host-level root access. Coordinate with cloud providers to verify host patching status in shared infrastructure deployments.
Conclusion and Next Steps
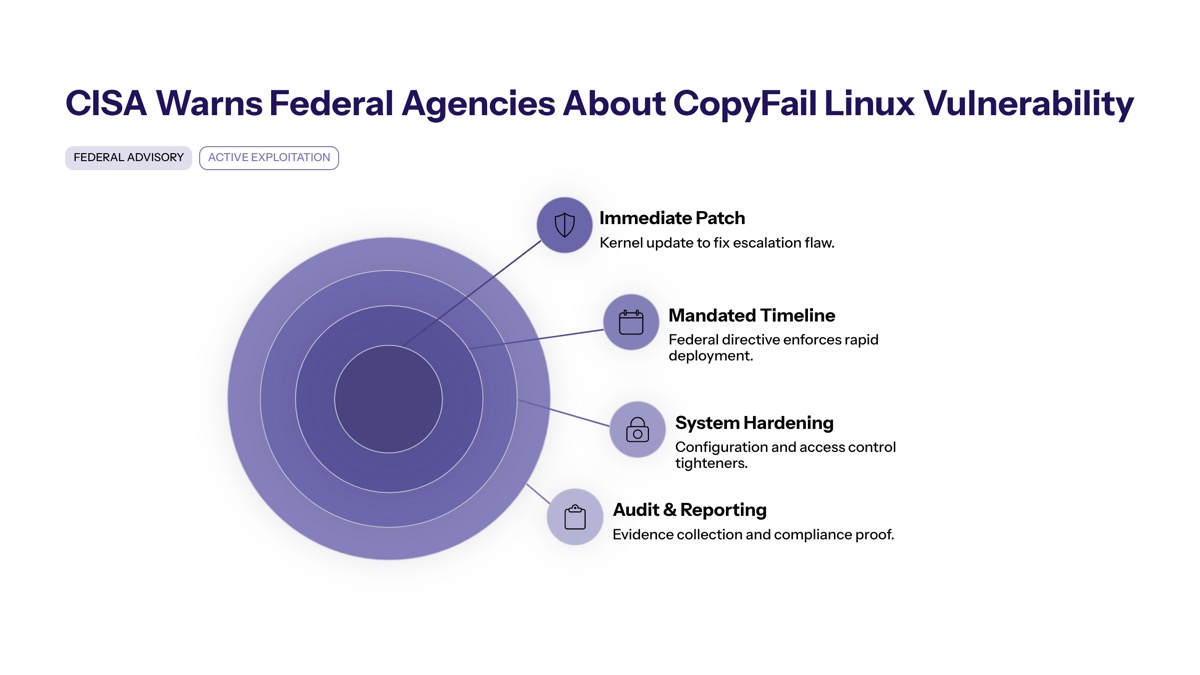
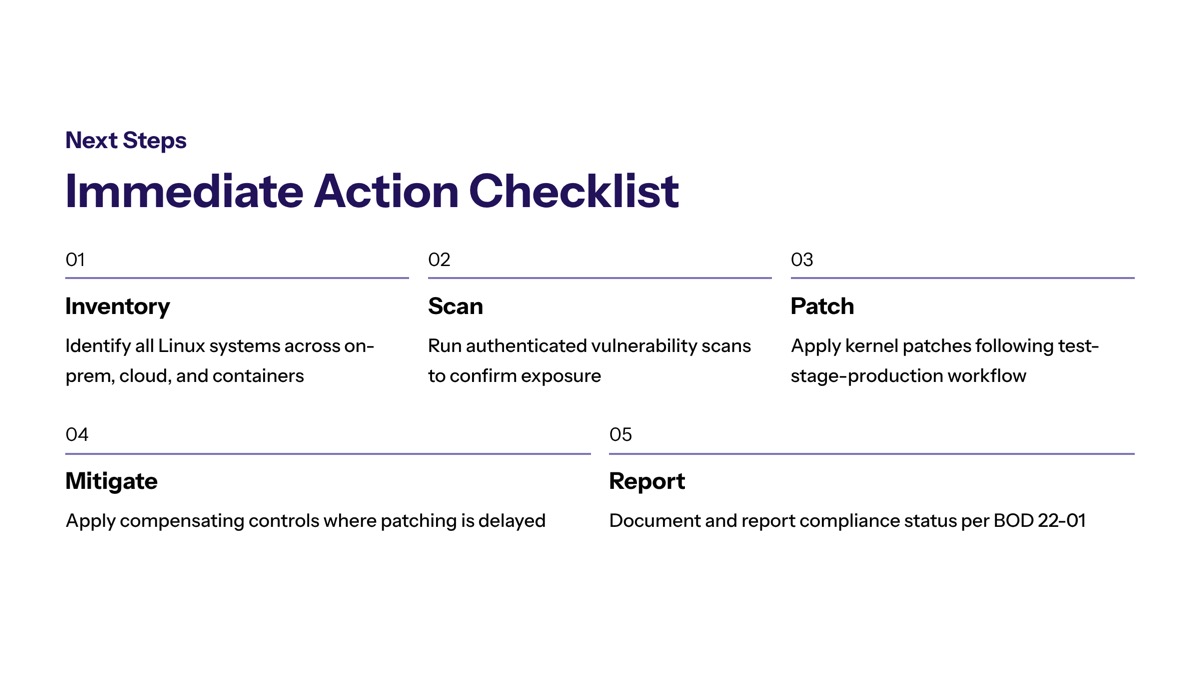
CVE-2026-31431 represents a critical Linux root privilege escalation vulnerability requiring immediate remediation across federal and enterprise environments. The May 15, 2026 deadline under BOD 22-01 creates a firm compliance boundary for federal agencies, while the active exploitation status makes rapid response essential for all organizations operating Linux infrastructure.
Take these immediate actions:
Complete comprehensive inventory of all Linux systems to identify affected systems running vulnerable kernel versions
Develop patch deployment plans prioritizing internet-facing systems, container hosts, and multi-tenant environments
Implement temporary mitigations for systems requiring extended maintenance windows
Document all remediation activities for compliance reporting and audit requirements
Establish ongoing monitoring for privilege escalation attempts targeting the Copy Fail vulnerability
Related security considerations include broader Linux kernel vulnerability management practices, container security hardening, and integration of the KEV catalog into organizational vulnerability prioritization frameworks. The reliable nature of this exploit—requiring no race conditions and working across major distributions—underscores the importance of rapid patching for future kernel vulnerabilities.
Additional Resources
Organizations should reference these authoritative sources for ongoing updates:
CISA KEV Catalog: Access at cisa.gov/known-exploited-vulnerabilities-catalog for current vulnerability listings and remediation deadlines
Vendor Security Bulletins: Ubuntu, Red Hat, SUSE, and Amazon Linux maintain security advisory pages with distribution-specific patch guidance
BOD 22-01 Documentation: Full directive text and compliance guidance available through CISA’s directives page for federal agency reference
Kernel Patch Details: Upstream commit a664bf3d603d contains the technical fix, available through kernel.org for organizations building custom kernels