Pentagon Uses Anthropic Mythos to Patch US Government Cybersecurity Gaps
The Pentagon deploys Anthropic’s Mythos to find and patch software vulnerabilities across US government systems at machine speed, marking one of the most significant applications of frontier models for national defense cybersecurity. This deployment occurs under Project Glasswing, a restricted initiative that allows select organizations to use Anthropic’s Mythos model for detecting decades-old vulnerabilities embedded in browsers, operating systems, and critical digital infrastructure.
This article covers the Pentagon’s implementation strategy, the capabilities driving this deployment, and the complex supply chain dynamics that make this situation unprecedented. The scope spans from the February 2026 supply chain risk designation through current operations in May 2026, examining what this means for federal cybersecurity modernization and regulated enterprise teams facing similar legacy system challenges. Target readers include CTOs, CISOs, and technology leaders in government, defense, financial services, and critical infrastructure sectors who must balance immediate security needs against long-term vendor risk management.
The Pentagon is utilizing Anthropic’s Mythos as part of Project Glasswing to patch cybersecurity gaps, allowing for the detection of vulnerabilities at machine speed—while simultaneously planning to ditch the firm and transition to alternative suppliers like OpenAI and Google in coming months.
After reading this article, you will understand:
How Mythos autonomously discovers decades-old security flaws in government systems
The strategic rationale behind deploying tools from a company labeled a supply chain risk
Practical implementation architecture and security controls governing access
Lessons applicable to enterprise cybersecurity modernization in regulated industries
Risk mitigation strategies for managing vendor transitions without creating cyber gaps
Understanding Anthropic Mythos and Government Cybersecurity Gaps
The relationship between AI-powered vulnerability detection and legacy government systems represents a fundamental shift in how organizations approach cybersecurity. Traditional security audits require weeks of expert analysis to identify flaws in complex codebases. Mythos compresses this timeline dramatically, identifying vulnerabilities that have persisted undetected for decades across federal infrastructure.
What Is Anthropic Mythos
Anthropic’s Mythos Preview represents a frontier AI model class positioned above the Claude model family, including previous iterations like Opus and Sonnet. This AI model requires significant compute infrastructure to operate and delivers capabilities specifically optimized for autonomous vulnerability discovery in software systems.
Mythos can autonomously find decades-old security flaws embedded in web browsers, digital infrastructure, and core operating systems like Linux. The model has been shown to identify and reproduce exploits for zero-day vulnerabilities with high accuracy, including detecting a 27-year-old vulnerability in OpenBSD that traditional security audits had missed entirely. Mythos excels at creating “exploit chains” by stringing together separate vulnerabilities, simulating real-world cyberattacks to aid defensive teams.
For enterprise security teams, this capability translates to identifying attack surfaces that human analysts might take months to discover—if they discover them at all. The model’s ability to detect thousands of high-severity vulnerabilities across major operating systems and browsers demonstrates why the Pentagon views this technology as critical for national defense.
US Government Cybersecurity Infrastructure Challenges
Federal cybersecurity infrastructure faces a scale problem that traditional approaches cannot solve. Government systems span hundreds of millions of lines of code across DoD networks, civilian agencies, and critical infrastructure sectors. Many of these systems run on software stacks that have accumulated vulnerabilities over decades—flaws that remain unpatched because they were never identified.
The defense department’s challenge extends beyond simple detection. The window between vulnerability discovery and adversarial exploitation has compressed dramatically due to automation capabilities now available to nation-state actors and sophisticated threat groups. Mythos has the capability to identify and patch decades-old vulnerabilities across government infrastructure in a fraction of the time it traditionally takes, but this same capability introduces a dual-use risk that the Pentagon explicitly acknowledges.
This scale of exposure creates the strategic imperative driving current deployment decisions, connecting legacy infrastructure vulnerabilities to the AI-powered detection solutions now being implemented.
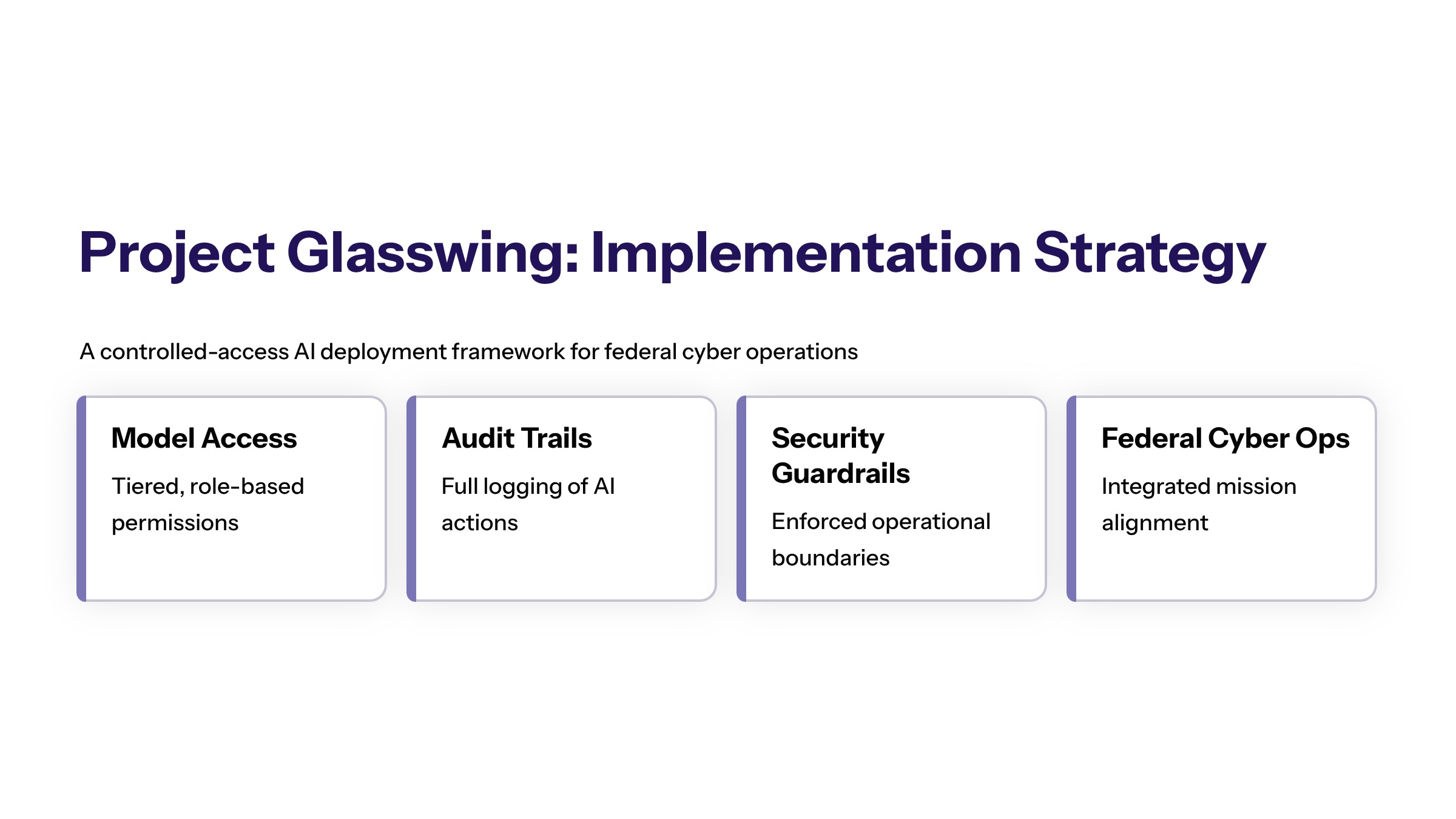
Project Glasswing Implementation Strategy
The Pentagon’s defensive cybersecurity approach leverages AI automation through Project Glasswing, a controlled access framework that balances capability deployment against security and supply chain considerations. This initiative represents a calculated decision to deploy frontier models from an AI company the government has formally designated a supply chain risk.
Deployment Architecture and Scope
Project Glasswing establishes technical controls governing how Mythos integrates within existing DoD security frameworks. The National Security Agency is reported to be using Mythos to secure Department of Defense networks, with controlled access protocols limiting which agencies and personnel can interact with the model.
Anthropic committed US$100 million in usage credits for Mythos under Glasswing, plus US$4 million to open-source security organizations. The initiative includes 11 core partner companies—Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks—with 40+ additional organizations granted access for critical infrastructure protection.
Security controls include usage limits, audit trails, and guardrails preventing applications in mass domestic surveillance or fully autonomous weapons systems. These restrictions contributed to the supply chain risk designation when the DoD requested their removal and Anthropic refused. Despite this friction, the deployment continues because immediate cybersecurity needs outweigh longer-term supplier concerns.
Vulnerability Detection Capabilities
Real-world performance metrics validate the Pentagon’s deployment decision. The UK AI Security Institute’s red team evaluated Mythos using their “Last Ones” cyber-attack simulation—a 32-step enterprise-network attack path designed to test complex exploitation capabilities. Mythos completed the full 32-step sequence end-to-end in 3 out of 10 trials, achieving approximately 73% success on expert-level capture-the-flag and network exploit tasks.
In Mozilla’s Firefox testing, Mythos discovered 271 vulnerabilities in a single build. This detection speed compared to traditional security audits represents orders-of-magnitude improvement—what previously required weeks of expert analysis now executes in hours or days.
The Pentagon acknowledges the dual-use risk that faster remediation capabilities could also enable adversaries to exploit vulnerabilities more quickly. The deployment of Mythos could accelerate the speed at which both defense and adversaries can identify and exploit vulnerabilities, creating a dynamic where patching speed becomes existentially important.
Integration with Existing Security Operations
Mythos findings integrate with existing vulnerability management workflows through structured reporting and prioritization frameworks. Human security analysts remain responsible for patch deployment, remediation verification, and risk assessment decisions—the AI model performs detection while humans execute response.
The use of AI models like Mythos could force IT teams to compress traditional multi-week patching timelines into mere days due to overwhelming patch workloads. This operational pressure requires organizations to pre-position remediation capabilities and establish rapid response protocols before deploying frontier detection tools.
This integration model provides the template for enterprise implementations while highlighting the organizational readiness requirements that precede effective AI-powered vulnerability management.
Supply Chain Risk Management and Supplier Transition
The Pentagon’s “deploy while ditching” approach to Anthropic creates a paradox that illuminates broader procurement challenges in the AI era. The use of Mythos represents a temporary measure amid severe friction between the Department of Defense and Anthropic, yet operational necessity drives continued engagement.
Current Implementation Process
Pentagon officials view the current access to Mythos as a temporary strategic advantage, anticipating that similar capabilities will soon emerge from other providers. This assessment shapes a structured transition process:
Deploy Mythos for critical vulnerability detection: Despite the supply chain risk designation from the Trump administration in February 2026, the Pentagon continues to pay for access to avoid leaving known vulnerabilities unpatched.
Maintain controlled access while evaluating risks: DoD Chief Technology Officer Emil Michael characterized this as a “national security moment” requiring temporary utilization of capable tools regardless of supplier classification.
Develop transition timeline to alternative suppliers: The Pentagon’s usage occurs while preparing a transition to cybersecurity-focused models from OpenAI, Google, and other providers expected to deliver comparable capabilities.
Execute supplier switch without disrupting operations: Plans to remove Anthropic’s products from DoD systems in coming months must avoid creating cyber gaps during the transition period.
Anthropic is involved in litigation against the U.S. administration regarding its blacklisting, contending that its technology is vital for national defense. Portions of the supply chain risk designation are temporarily stayed by court action as of late March 2026, adding legal complexity to procurement decisions.
Alternative AI Provider Evaluation
The Pentagon’s procurement strategy involves temporary dependency on Anthropic’s Mythos to address immediate cybersecurity vulnerabilities while planning for transition to alternative suppliers. Current evaluation focuses on capability matching and operational continuity.
Capability | Anthropic Mythos | OpenAI Models | Google Alternatives |
|---|---|---|---|
Complex Attack Completion | 3/10 full success (32-step sequences) | Under evaluation | Under evaluation |
Vulnerability Detection Speed | Machine speed scanning | Comparable processing speed expected | Pending benchmark results |
Zero-Day Exploit Reproduction | High accuracy demonstrated | Capability under assessment | Capability under assessment |
Government Approval Status | Supply chain risk designation | DoD agreements in place | Evaluation pending |
Access Restrictions | Guardrails on surveillance/weapons | Terms under negotiation | Terms under negotiation |
Pentagon officials anticipate that OpenAI, Google, and other providers will deliver comparable vulnerability detection capabilities, though current public benchmarks do not yet demonstrate Mythos-equivalent performance on complex enterprise-network attack simulations.
The defense department’s approach underlines a strategic decision to deploy AI models for cybersecurity while managing risks associated with limited supplier options—a pattern likely to influence procurement strategies across private companies and allied nations.
Common Implementation Challenges and Solutions
These challenges affect government agencies and regulated enterprises alike. US banks, Morgan Stanley, and other financial institutions face similar decisions when evaluating frontier AI tools for security operations.
Compute Infrastructure and Scaling Limitations
Running Mythos requires significant compute infrastructure for scanning large codebases and evaluating potential exploits. Not all agencies have infrastructure ready to scale to enterprise-wide usage, creating bottlenecks in deployment.
Solution: Implement controlled access and priority queuing systems that allocate compute resources based on criticality assessments. Pre-position infrastructure through cloud partnerships (AWS, Google Cloud, Microsoft Azure) that can scale dynamically. For organizations without immediate infrastructure, consider phased deployment starting with highest-risk systems while building capacity.
Balancing AI Capability with Security Controls
The same vulnerability-finding capabilities that serve defense can serve offense if access is uncontrolled. Mythos can generate proof-of-concept exploits, creating dual-use risks that require governance frameworks.
Solution: Establish clear governance frameworks specifying permitted use cases, access controls, and audit requirements before deployment. Define acceptable use boundaries that prevent misuse while enabling defensive operations. Implement logging and monitoring that tracks all model interactions, enabling forensic review and compliance verification.
Managing Supplier Transition Without Security Gaps
Given the Pentagon’s intention to phase out Anthropic tools in coming months, transition risks include capability gaps if alternatives lack Mythos performance, workflow disruption for teams dependent on current tools, and potential adversary exploitation during transition periods.
Solution: Maintain parallel evaluation of alternative providers throughout deployment. Document integration points and dependencies to enable rapid switching. Establish performance baselines that alternatives must meet before transition execution. Build internal capabilities that reduce single-vendor dependency regardless of which suppliers are engaged.
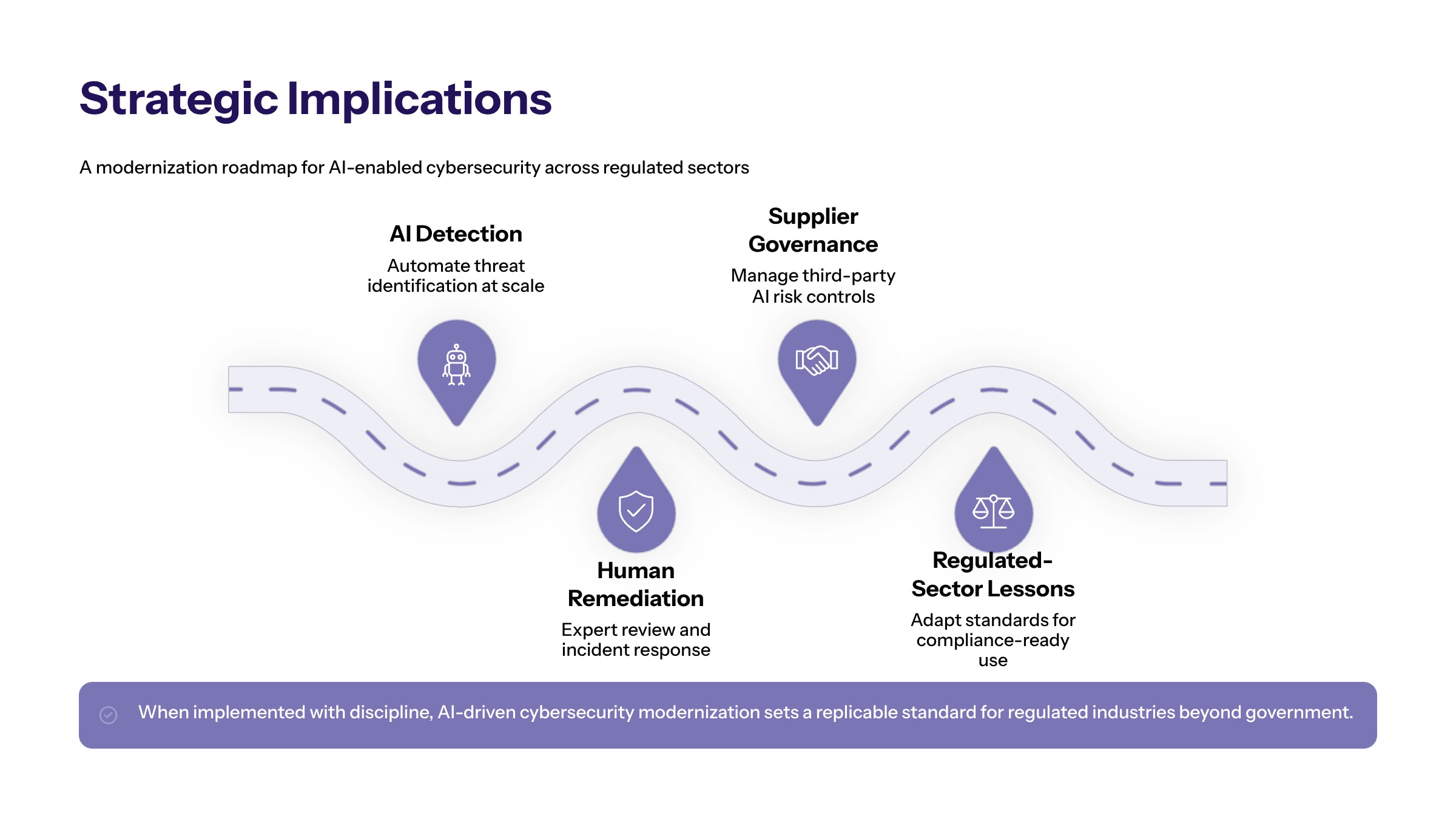
Conclusion and Strategic Implications
The Pentagon’s deployment of Anthropic’s Mythos demonstrates practical AI application for large-scale cybersecurity modernization while highlighting the complex tradeoffs involved in frontier model procurement. The utilization of advanced AI tools introduces a paradigm shift in national security by improving defensive speed while creating operational friction with suppliers over guardrails and acceptable use restrictions.
The Pentagon’s decision to use Mythos reflects a strategic dilemma where they utilize a tool from a company labeled as a supply chain risk—a decision driven by the calculation that leaving known vulnerabilities unpatched creates greater risk than supplier dependency. This approach may influence similar strategies in private companies, US banks, and allied governments facing comparable modernization challenges.
Immediate actionable insights for enterprise teams:
Evaluate AI-powered vulnerability detection for legacy system modernization, recognizing that frontier models can identify flaws that traditional audits miss
Develop supplier risk management frameworks that accommodate temporary dependency while building transition capabilities
Plan compute infrastructure requirements before deploying frontier AI tools to avoid bottlenecks that limit effectiveness
Establish governance frameworks proactively that define acceptable use boundaries and prevent the friction that complicated Pentagon-Anthropic relations
For regulated industry teams, the Pentagon’s experience offers a template: deploy capable tools when security needs demand it, but build the organizational infrastructure—governance, alternatives, transition plans—that prevents vendor lock-in from becoming strategic vulnerability.
Additional Resources
UK AI Security Institute frontier AI evaluation reports and “Last Ones” benchmark methodology
DoD AI partnership frameworks and supplier evaluation criteria for defense applications
Enterprise AI governance templates adapted for regulated industries including financial services and critical infrastructure
Open-source security organization resources supported through Project Glasswing funding