US Banks Rush to Fix Vulnerabilities Flagged by Anthropic Mythos AI
Major US banks are urgently addressing thousands of cybersecurity vulnerabilities discovered by Anthropic’s Mythos AI model, a development that has transformed banking security operations since early April 2026. The release of Claude Mythos Preview under Project Glasswing has prompted the country’s largest lenders to accelerate patching cycles, coordinate with regulators, and fundamentally rethink their approach to cyber risk management.
This article covers which financial institutions have direct access to Mythos, what types of system weaknesses are being flagged, the timeline for urgent repairs, and how the banking sector is coordinating its response. The target audience includes IT security leaders, bank executives, and cybersecurity professionals working in financial services who need to understand both the technical capabilities of this AI model and its operational implications.
Major US banks including JPMorgan Chase, Goldman Sachs, and Morgan Stanley are working around the clock to patch hundreds to thousands of security vulnerabilities that Anthropic’s Mythos AI discovered in their systems—many of which had remained hidden for decades in legacy systems and open source code dependencies.
Key outcomes from this article:
Understanding of Mythos technical capabilities and how they differ from traditional security tools
Comprehensive view of the banking industry response and implementation strategies
Clarity on regulatory coordination and remediation processes
Practical insights into common challenges and solutions for both larger banks and smaller institutions
Understanding Anthropic Mythos and Its Vulnerability Detection Capabilities
Mythos is Anthropic’s advanced AI model specifically designed for cybersecurity vulnerability discovery, released in research preview around April 7, 2026. Unlike traditional static code analyzers or fuzz testing tools, Mythos combines automated reasoning, pattern recognition, and generative exploit crafting to identify software vulnerabilities at machine speed rather than human speed.
Core Technical Capabilities
The AI model Mythos is particularly adept at identifying and connecting minor vulnerabilities into serious weaknesses, which human auditors often miss. Where conventional security tools find individual flaws, Mythos excels at uncovering issues that chain together—combining race conditions, memory safety violations, privilege escalation paths, and sandbox escapes into exploitable attack sequences.
Mythos produces working exploits, not just vulnerability reports. Documented examples include a web browser exploit chaining four vulnerabilities together, root access via remote code execution in FreeBSD NFS servers, and local privilege escalation on Linux through subtle race conditions that bypass Kernel Address Space Layout Randomization. The model has identified thousands of vulnerabilities in US bank systems, significantly affecting aging software that had been considered secure through years of manual auditing.
Project Glasswing Access Model
Access to Mythos operates through Project Glasswing, a controlled rollout limited to approximately 40 select organizations. These include major technology companies like Amazon, Apple, and Microsoft, critical infrastructure vendors, the Linux Foundation, and a small cohort of US banks. JPMorgan Chase was confirmed as the first bank to receive access, with Goldman Sachs, Morgan Stanley, and Bank of New York Mellon following by early May 2026.
Foreign governments are excluded from this initial rollout, and Anthropic has implemented strict access controls and safety gates to prevent misuse. By May 8, 2026, no European banks had confirmed access to the model.
Cost and Accessibility Barriers
The pricing structure for AI tools like Mythos presents a significant barrier for smaller banks. The cost of using the Claude Mythos AI model is $25 per million tokens for input and $125 per million tokens for output, making it five times more expensive than Anthropic’s Opus 4.7 model. This costly Mythos AI tool requires substantial computing power that many smaller institutions lack.
Anthropic has pledged $100 million in credits to support partners and customers using Mythos, which is intended to cover substantial usage during its research preview phase. However, this primarily benefits Glasswing partners and other Mythos customers with direct access rather than the broader banking sector.
The overwhelming capability gap between those with access and those without has created a two-tier security landscape in financial services, prompting urgent repairs and new coordination mechanisms across the industry.
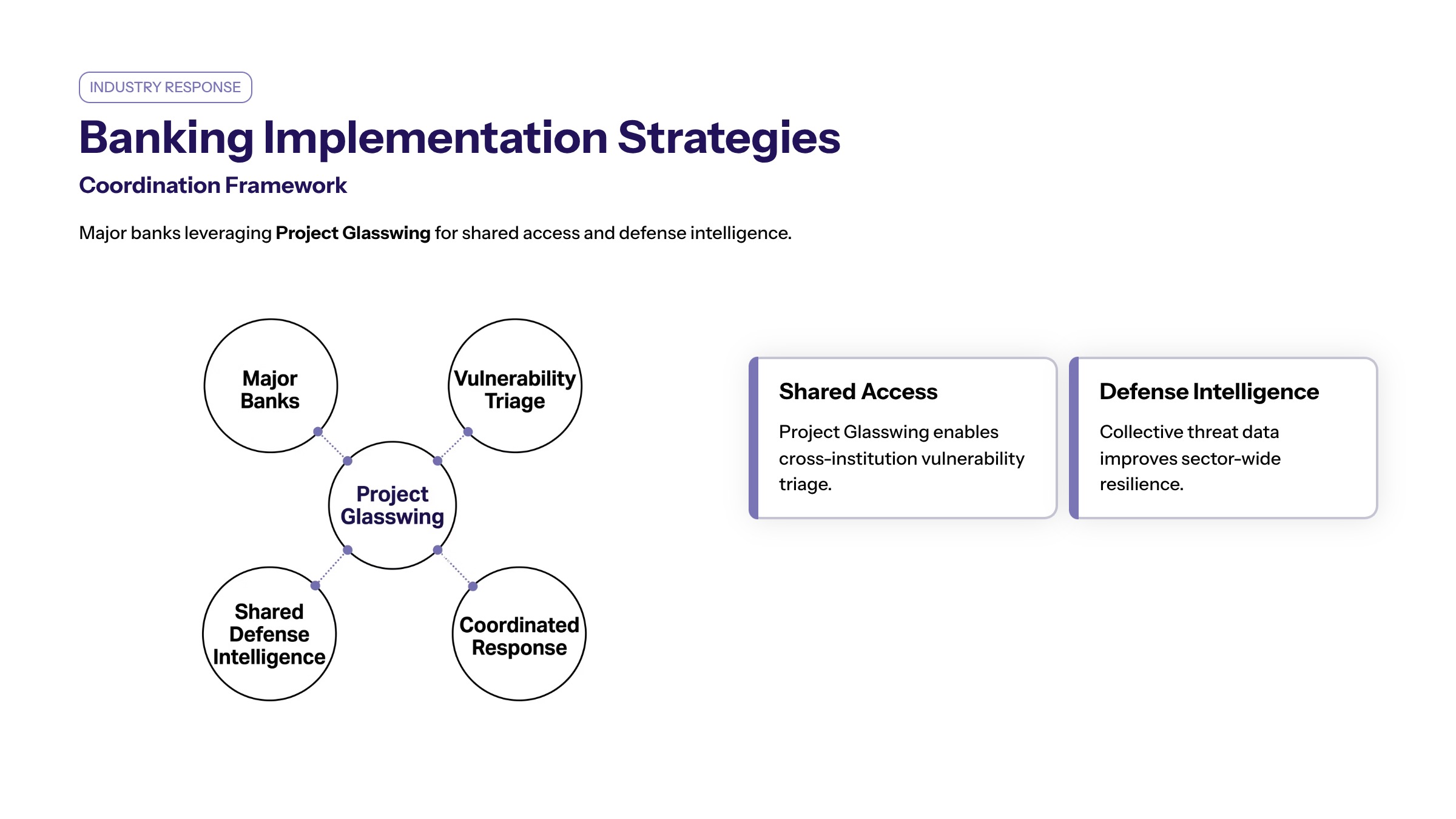
Banking Industry Response and Implementation Strategies
When major banks received Mythos access through Project Glasswing, company executives quickly recognized both the opportunity and the scope of the challenge. The model’s ability to scan entire codebases and connect complex data points faster than human analysts has fundamentally changed how these institutions approach vulnerability management.
Major Bank Participation
JPMorgan Chase, Goldman Sachs, Morgan Stanley, and Bank of New York Mellon have confirmed their participation in the early access program. These institutions are coordinating with cybersecurity firms like CrowdStrike to develop a whole methodology for integrating Mythos findings into their existing security operations.
Adam Meyers and other security strategist leaders at partnering firms have worked with bank security teams to establish protocols for triaging the massive volume of discoveries. Several sources familiar with the implementations describe teams that spent a solid entire weekend conducting initial scans and emergency triage sessions.
Vulnerability Discovery Scale
Banks are experiencing an overwhelming volume of flagged vulnerabilities, with some institutions reporting hundreds to thousands of issues needing urgent fixes. Anthropic’s Mythos AI model has exposed thousands of previously unknown “zero-day” security flaws and long-standing software vulnerabilities that had persisted through years of traditional auditing.
Many vulnerabilities detected by Mythos exist in connections with vendor partners and core banking platforms, not just internal systems. This has expanded the scope of remediation well beyond what banks initially anticipated, requiring coordination with external software providers and open source maintainers.
Information Sharing with Smaller Banks
Major institutions with access to Mythos are sharing defense data to help protect regional and community banks. This approach recognizes that systemic cyber risk threatens the entire banking sector, not just individual institutions.
Financial institutions are utilizing collaborative information sharing to enhance security across the banking sector. Larger banks are helping inform smaller banks about critical vulnerability classes, recommended patches, and defensive configurations—even when they cannot share the specific Mythos outputs due to licensing restrictions.
As Nitin Seth and other banking technology leaders have noted, this collaborative approach represents a shift from competitive secrecy to collective defense in banking security.
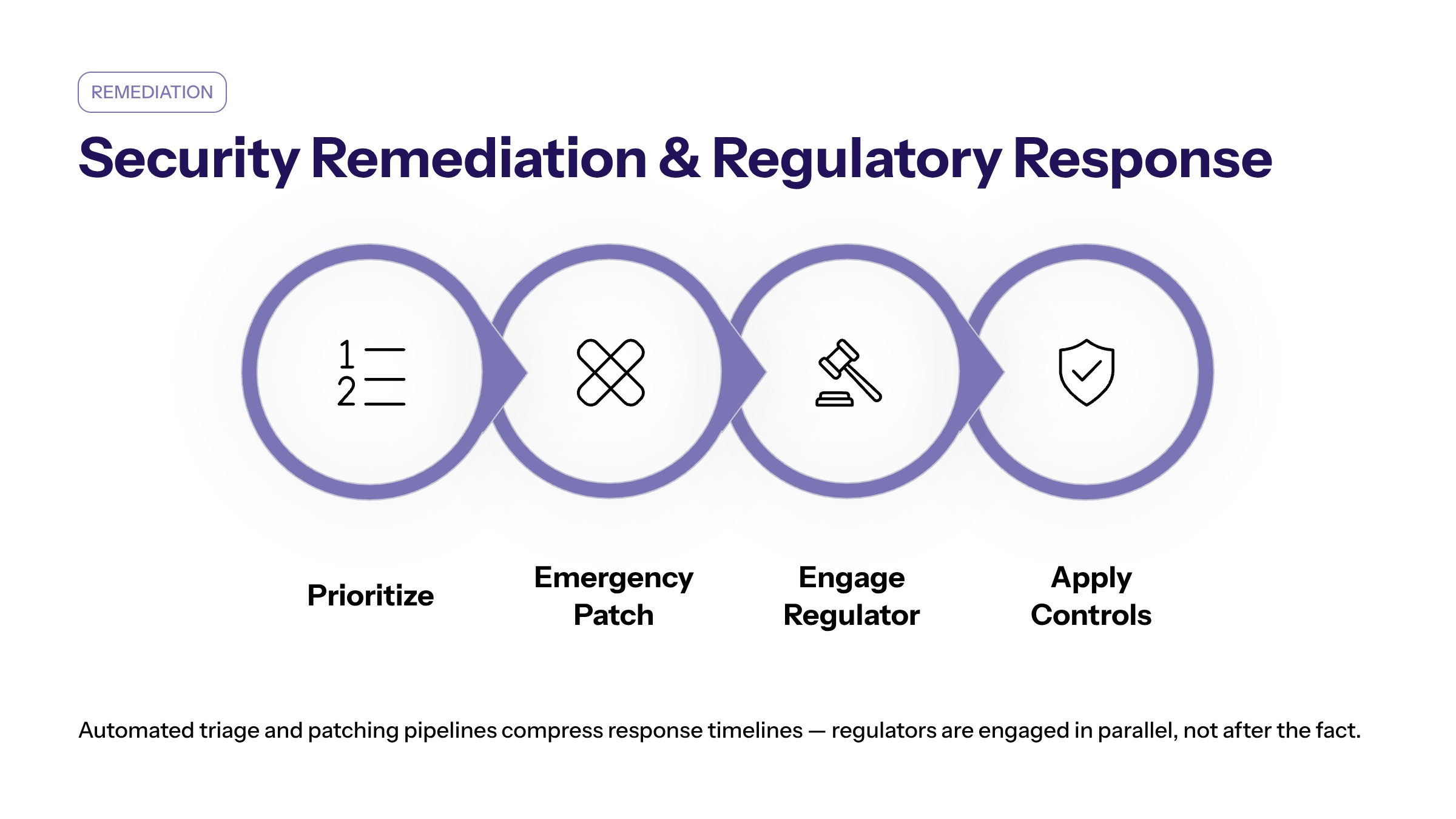
Security Remediation Processes and Regulatory Response
The urgent nature of vulnerabilities flagged by Mythos has forced banks to compress traditional patching cycles and accept more frequent system downtimes. Banks are shifting from human-speed defense to machine-speed remediation, reducing patch times from weeks to days in many cases.
Patch Management Procedures
Vulnerabilities are triaged by severity, with those enabling remote code execution, privilege escalation, or multi-flaw chains receiving top priority. Banks are focusing first on internet-facing software, critical backend systems, operating system kernels, browser components, and third-party dependencies across major operating systems.
Emergency change management processes have been activated for high-risk systems, with deviations from normal change windows including night and weekend patching with fast-track approvals by security and risk committees. Testing protocols ensure patches don’t disrupt banking operations, though the compressed timelines have increased operational risk.
Banks are facing immediate pressure to retire legacy technology and update systems that are past their end-of-software-support lifespan. Some institutions have brought in external vendors and specialized cybersecurity firms to assist with the rapid rollout of fixes across their technology estates.
Regulatory Agency Coordination
Federal regulators have responded with unusual urgency to the Mythos disclosure. Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell convened meetings with bank CEOs to assess readiness and coordinate responses. A senior bank regulatory official described the sessions as focused on ensuring systemic preparedness across institutions classified as “systemically important.”
Regulators are focusing on the accelerated nature of vulnerabilities exposed by AI tools like Mythos, recognizing that the traditional pace of regulatory guidance may be insufficient. The FDIC has begun developing guidance on AI-assisted vulnerability management for smaller institutions, though specific directives have not yet been publicly issued.
Interagency coordination emphasizes that Mythos represents a significant test for the banking sector’s aging technology, highlighting the need for rapid adaptation to machine-speed cyber risks. Banks are transitioning to continuous, AI-driven security scans instead of periodic penetration testing, fundamentally changing their security posture.
Common Challenges and Solutions
As banks implement Mythos-informed remediation strategies, several recurring challenges have emerged across the industry. Reuters reported on many of these difficulties, citing sources familiar with implementation efforts at multiple institutions.
Resource Constraints at Smaller Banks
Smaller banks face significant barriers to implementing AI tools like Mythos due to high costs and the need for substantial computing power, which they often lack. Without direct access, these institutions rely instead on larger institutions to share findings and recommendations to help them address vulnerabilities in their systems.
The solution emerging across the industry involves larger banks systematically sharing data about vulnerability classes, affected software versions, and recommended mitigations. Several industry consortia and threat intelligence platforms are facilitating this information flow, ensuring that smaller institutions can prioritize their limited remediation resources effectively.
System Downtime During Critical Patches
Banks may require more frequent system downtimes to address the volume of issues being uncovered, sometimes taking systems offline for extended periods during critical updates. This creates tension between security urgency and operational continuity.
Institutions are implementing scheduled maintenance windows with enhanced customer communication strategies to minimize service disruption. Many banks have established tiered response protocols that allow critical customer-facing systems to remain operational while backend components undergo patching.
Speed vs. Security Trade-offs
Balancing rapid vulnerability remediation with thorough testing remains one of the most significant challenges. The pressure to fix scores of vulnerabilities quickly risks introducing new security problems or operational instability.
Banks are addressing this through expanded staging environments, automated regression testing, and enhanced rollback capabilities. Some institutions have created dedicated rapid-response teams that operate parallel to normal development workflows, allowing faster deployment while maintaining testing rigor for production systems.
Conclusion and Next Steps
US banks are successfully leveraging Mythos to strengthen their cybersecurity posture, though the scale of discovered vulnerabilities has made this a wake up call for the entire sector. The long standing assumption that well-audited systems were secure has been challenged by an AI model that operates at machine speed, connecting vulnerabilities that human analysts would have missed.
Oh boy—the scope of remediation work ahead remains substantial. Anthropic’s warning that adversaries may develop comparable capabilities within 6 to 12 months adds urgency to current counter adversary operations and bank defense initiatives.
Immediate next steps for financial institutions:
Establish AI-assisted vulnerability management programs, either through direct Mythos access or partnerships with institutions that have it
Strengthen incident response capabilities to handle the compressed timelines that AI-discovered vulnerabilities require
Enhance coordination with cybersecurity partners and industry information-sharing platforms
Accelerate retirement of legacy systems and software upgrades for components past end-of-support
Related topics worth exploring include AI-powered threat detection beyond vulnerability scanning, evolving banking cybersecurity compliance requirements, and financial sector incident response planning in an era of machine-speed threats.
Additional Resources
Federal banking regulator guidance on AI cybersecurity tools and emerging threat landscapes
Banking industry cybersecurity frameworks including updated vulnerability management protocols
Anthropic Mythos technical documentation for qualified institutions participating in Project Glasswing
Industry consortia platforms for sharing vulnerability intelligence between major bank and smaller bank partners